But the fundamentals have not changed.
An alarm system works like a chain. It may have strong sensors, a good control panel, and a loud siren, but one weak real-world link can reduce the value of the entire system.
That is where many homeowners, small businesses, and even some companies still get it wrong.
An alarm system is like a chain: it is only as strong as its weakest real-world link.
A modern alarm system may be easier to install than older systems, but easier installation does not automatically mean stronger protection. It should be understood as one layer inside a broader professional security system. The real value depends on design, placement, response, and how the system behaves when something actually goes wrong.
What Is an Alarm System Really?
At its core, an alarm system is not just about detection.
It is about triggering a response.
Detection without response is not protection.
A motion sensor can detect movement. A door contact can detect entry. A glass-break sensor can detect impact or acoustic patterns. But unless someone reacts quickly enough, the system has failed its purpose.
This is the difference between a device that makes noise and a security system that helps protect property.
For a wider view of how cameras, recording, alarms, and access control work together, read our guide to what security technology means in practice.
The Evolution From Legacy Systems to Modern Security
Based on real field experience, older alarm systems often required hardwired infrastructure, specialized installation tools, dedicated control panels, and professional-only configuration.
They were powerful in their time, but they were rigid. Expanding them, relocating sensors, or changing the installation often required more time, more tools, and more technical knowledge.
- 1Hardwired infrastructure
- 2Specialized installation tools
- 3Dedicated control panels
- 4Professional-only configuration
Today’s systems are different.
Modern alarm systems are often wireless, app-connected, remotely configurable, and capable of sending real-time alerts directly to a phone or monitoring service.
- ✓Wireless sensors are easier to place and expand.
- ✓Mobile apps provide real-time alerts and remote control.
- ✓Installation can be faster and less invasive.
- ✓Some systems can be deployed without heavy infrastructure.
Modern alarm systems are easier to install — but not automatically more secure.
Ease of installation has improved. But security still depends on how the system is designed and used.
Types of Alarm Systems
Alarm systems can be grouped in several ways. The most practical approach is to look at how they are installed, how alerts are handled, and whether someone is responsible for responding.
1. Wired Alarm Systems
Wired alarm systems use physical cabling between sensors, sirens, control panels, and other components. They can be reliable and stable, especially in permanent installations.
- ✓Reliable and stable when installed correctly
- ✓Harder to tamper with physically than many simple wireless systems
- ✓Best for larger buildings and long-term installations
2. Wireless Alarm Systems
Wireless alarm systems are faster to install and easier to expand. They are popular in homes, small businesses, rental properties, and retrofit projects where new cabling would be difficult or expensive.
- ✓Fast to install
- ✓Flexible and scalable
- !Battery status and wireless signal quality must be monitored
3. Monitored Alarm Systems
A monitored alarm system is connected to a monitoring center or security service. When the alarm triggers, an operator or service provider can take action.
An alarm system is only effective if someone responds to it.
This type of system is often best for high-value properties, commercial locations, professional security environments, and situations where response speed matters.
4. Unmonitored or Self-Monitored Systems
Self-monitored systems send alerts to the owner’s phone or app. This can be useful, but there is no guaranteed response.
If the owner is sleeping, driving, abroad, in a meeting, or without internet access, the alarm may be noticed too late.
5. Smart Alarm Systems
Smart alarm systems are integrated with mobile apps and often connect to smart home platforms. They are closely related to the broader category of smart security systems. They can offer remote control, notifications, logs, and automation features.
A smart alarm is not the same as a professional security system.
Smart features are useful, but professional protection still depends on planning, coverage, response, testing, and redundancy.
Real-World Weaknesses Most People Ignore
This is where theory ends and reality begins.
Based on my 26 years of law enforcement experience, the same patterns appeared again and again. Security systems often failed not because the technology was completely useless, but because the design ignored how people actually attack, bypass, misuse, or weaken the system.
Security systems do not fail only in manuals. They fail in real buildings, under real pressure, against real behavior.
Siren Placement Can Make or Break the System
Many alarm systems rely heavily on sirens. But siren placement is critical.
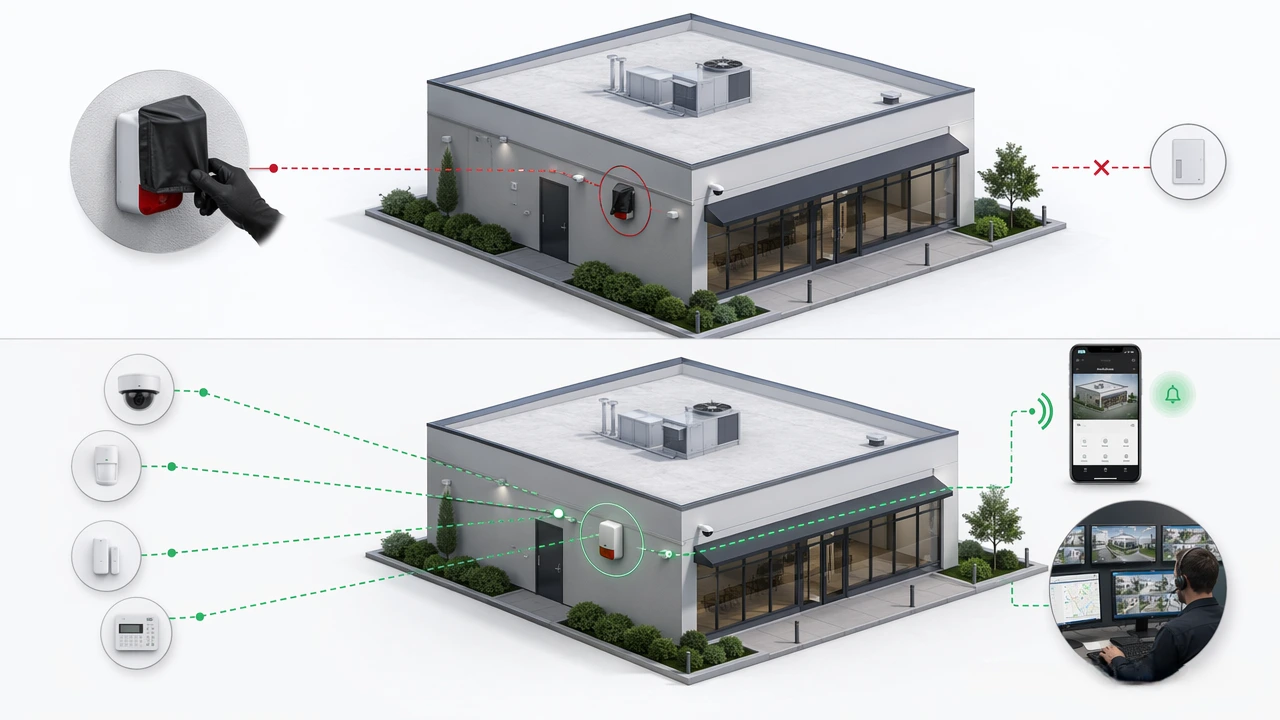
If the siren is easily reachable, externally exposed, and not backed by additional alerts, it can be neutralized very quickly.
- ×The siren is mounted too low.
- ×The siren is easy to reach from the ground or a simple ladder.
- ×The system depends only on sound.
- ×There is no mobile alert, monitoring service, or secondary notification path.
In real incidents, burglars have used simple physical methods to silence exposed sirens. Expanding foam can block or muffle the siren. Water can also be used to damage or neutralize poorly protected siren units.
This is not theory. This is practical field experience.
If the siren is accessible and there is no secondary alert, the system can be silenced instantly.
This is why modern systems should not rely on a single siren as the only meaningful alarm response. A siren can still be useful, but it should be one layer — not the whole strategy.
Alarm Codes Are Often Predictable
One of the most overlooked vulnerabilities is human behavior.
People often choose simple codes because they are easy to remember. Unfortunately, simple codes are also easier to guess, observe, share, and misuse.
- ×Straight-line patterns on the keypad
- ×Repeated digits
- ×Birth years or obvious numbers
- ×Codes shared with too many people
A typical example is a simple keypad pattern, such as a “middle row downward” style code. It feels convenient, but it creates a predictable pattern.
If everyone knows the code, there is no code.
A code that is shared with too many employees, contractors, relatives, neighbors, or temporary workers is no longer a strong security control. It becomes a common secret — and common secrets are weak.
Keypad Wear Can Reveal the Code
A detail many people never think about is keypad wear.
Physical usage leaves traces. Dirty, oily, worn, or polished keypad buttons can reveal which digits are used most often. In some cases, the pattern itself becomes visible.
- !Frequently used digits may become visibly cleaner or more worn.
- !Finger marks can reduce the number of likely combinations.
- !Simple patterns become easier to reconstruct.
In real-world situations, this kind of small detail has helped attackers narrow down possible alarm codes much faster than people would expect.
This is another reason why alarm codes should be changed regularly, access should be limited, and where possible, systems should use individual user codes rather than one shared code.
Why Modern App-Based Alarm Systems Are Stronger
Modern alarm systems address many of these weaknesses by reducing reliance on one physical alert method.
Instead of depending only on a siren, app-based systems can send real-time notifications, log events, show system status, and sometimes connect to monitoring services. In many properties, these systems work best when combined with security camera systems and reliable recording.
- ✓Alerts can be sent directly to mobile devices.
- ✓Multiple notification channels reduce single-point failure.
- ✓Remote control can support faster decisions.
- ✓Logs and histories can show what happened and when.
- ✓Monitoring integration can create a stronger response path.
Redundancy is what turns detection into real protection.
The key is layered alerting. A siren may scare someone away. A phone alert may notify the owner. A monitoring service may support response. Logs may help later investigation.
One layer can fail. Multiple layers are harder to defeat.
Components of a Modern Alarm System
A complete alarm system usually includes several parts. The exact setup depends on the property, risk level, budget, and response plan.
- 1Control panel or central unit — the core device that manages the system.
- 2Motion sensors — detect movement in selected areas.
- 3Door and window contacts — detect opening events.
- 4Glass-break sensors — detect the sound or vibration of breaking glass.
- 5Internal and external sirens — create audible alerts.
- 6Mobile app integration — provides remote alerts and control.
- 7Optional monitoring service — adds a human response layer.
But technology alone is not enough.
Design and usage determine real security.
Common Mistakes When Choosing an Alarm System
Many alarm system failures begin before the first sensor is installed. The problem often starts with the wrong buying criteria.
- 1Choosing based on price only
- 2Ignoring who will respond to the alarm
- 3Using weak, shared, or predictable codes
- 4Placing the siren where it can be easily reached
- 5Over-relying on smart features without testing response
- 6Not testing the system under realistic conditions
- 7Forgetting battery maintenance in wireless systems
- 8Failing to update user codes when staff or access changes
The best alarm system is not always the most expensive one. It is the one that matches the risk, covers the right areas, alerts the right people, and supports a real response.
Practical Alarm System Planning Checklist
Before choosing or installing an alarm system, answer these questions:
- ✓What exactly must the system protect?
- ✓Which entry points are most likely to be used?
- ✓Where should the siren be placed so it is not easily disabled?
- ✓Who receives the alert?
- ✓Who responds if the owner is unavailable?
- ✓Are there multiple alert paths, not just one siren?
- ✓Are alarm codes individual, strong, and controlled?
- ✓Will keypad wear or shared access weaken the system?
- ✓How often will the system be tested?
- ✓What happens when power, internet, or batteries fail?
This checklist is not about making the system complicated. It is about making the system realistic.
Final Thought
After decades of real-world experience, one thing remains clear:
Security systems do not fail because of technology alone. They fail because of assumptions.
Modern alarm systems are more accessible than ever. They are easier to install, easier to manage, and often much stronger than older systems when they are planned correctly.
But real protection still requires proper setup, realistic thinking, controlled access, good siren placement, multiple alert paths, and an understanding of how systems fail in practice.
Because in security, what matters is not only what the system is designed to do.
What matters is what it actually does when something goes wrong.
Continue with practical security technology guides.
Explore more SecurityTechLab articles on alarm systems, CCTV cameras, NVR recording, smart security, and professional security technology.
Explore Alarm System Guides